Securing your IS to sustainably protect your business
In a context of growing cyber threats, an insufficiently secured information system exposes the organization to operational, financial, and reputational risks. Implementing adapted and effective mechanisms becomes essential.
Managed cyber risks
Reduction of attack exposure through protection and monitoring mechanisms adapted to your IS.
Business continuity assured
Ability to quickly detect incidents and react effectively to limit service interruptions.
Real-time monitoring
Continuous IS monitoring to track threats, prioritize actions, and make informed decisions.
/ A comprehensive approach to secure and monitor your IS
Castelis takes a structured and continuous approach to securing information systems, from risk analysis to operational monitoring.
Assessment
Technical and organizational security audit to identify vulnerabilities and weaknesses.
Protection
Implementation of security mechanisms adapted to your uses and IS architecture.
Monitoring
Continuous system monitoring and proactive threat detection via a dedicated SOC.
Remediation
Incident management, vulnerability remediation, and continuous improvement of the mechanism.
/
Integrated and operational cybersecurity expertise
Castelis combines technical expertise, reference tools, and continuous monitoring to secure your cloud and application infrastructures, while adapting to your operational constraints.
Cloudflare partnership and always-on protection
24/7 SOC with incident detection and response
Cloud security and DevSecOps approach
Penetration tests and regular audits

Concrete solutions to protect your information system
Castelis deploys comprehensive cybersecurity solutions to protect, monitor, and manage your information system against increasingly sophisticated threats.
Security audit & governance
Comprehensive assessment of your security posture, priority definition, and implementation of governance adapted to your challenges and constraints.
Cloud security & Zero Trust
Protection of cloud environments through Zero Trust approaches, IAM, and access and flow security.
Web security & SOC monitoring
Protection of exposed applications and continuous monitoring, with threat detection and security incident management.
SIEM & event correlation
Centralization and analysis of security events to detect suspicious behaviors and strengthen response capability.
Email & phishing protection
Messaging security against phishing, identity theft, and malware.
Application penetration tests
Penetration tests to identify vulnerabilities and assess system resistance.
/
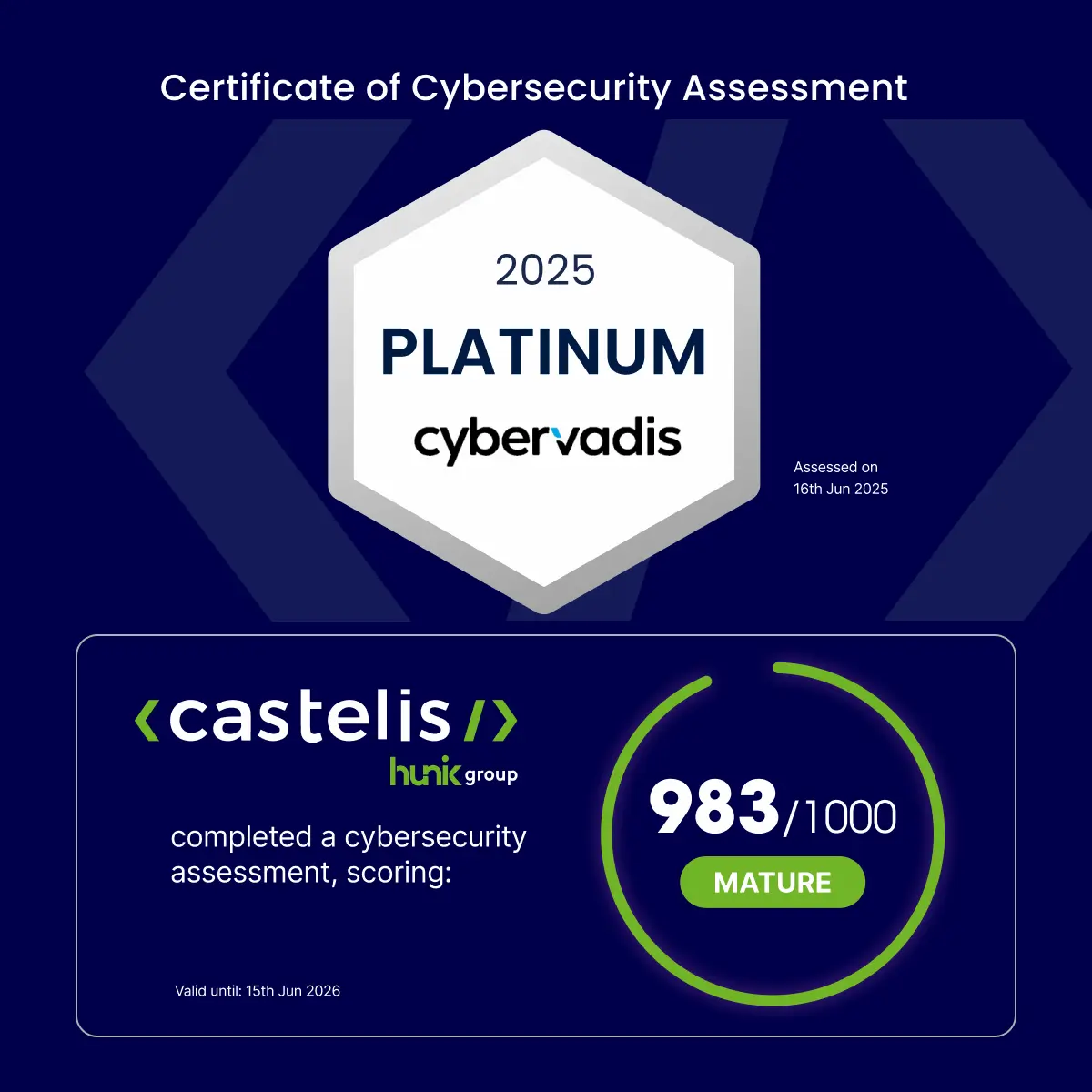
Cybersecurity expertise recognized by CyberVadis
Castelis obtained the CyberVadis 2025 Platinum medal with a score of 983/1000, attesting to a high level of cybersecurity maturity. This recognition is based on strict criteria covering governance, processes, and technical measures, and translates into reliable and proven practices in the service of your IS security.
High standards
Continuous improvement
A trusted partner committed to securing your IS
Castelis supports organizations in securing and monitoring their IS with a pragmatic, proven, and results-oriented approach.
Cybersecurity expertise
Proven mastery of security challenges, integrated into the real constraints of organizations.
Comprehensive approach
Present from audit to continuous monitoring, with no gap in responsibility to avoid blind spots in security.
Leading technology partnerships
Recognized and proven solutions, selected to be deployed, monitored, and maintained over the long term.
Long-term commitment
Continuous involvement by your side to evolve your security mechanisms in response to threats and IS transformations.
/
FAQ on IS security and monitoring
Attacks evolve constantly and can occur at any time. Continuous monitoring enables rapid detection of abnormal behavior, immediate reaction, and limiting the impact on business.
No. An audit identifies vulnerabilities at a given moment, but security relies on a continuous approach combining protection, monitoring, and permanent improvement.
Securing a hybrid or cloud IS relies on adapted approaches: Zero Trust, identity and access management, continuous monitoring, and integrating security from the design phase.
Let's talk about your project

