Our cloud & compliance expertise
We support CIOs and IT teams in the compliance and security of their cloud environments, combining governance, risk management, and technical documentation.
Cloud governance
Design and deployment of governance policies for your Azure, GCP, AWS, and hybrid environments, with cloud transformation support and associated training.
GDPR compliance
Audit and remediation of your cloud environments to ensure GDPR compliance: data protection policies, access traceability, and continuity of compliant practices.
Cloud risk management
Analysis of cloud vulnerabilities (intrusion, crash, data leaks) and development of action plans to manage, reduce, and anticipate risks according to ISO 27001 and NIST standards.
ISO compliance audit
Audit of security documents and processes in place to ensure their compliance with applicable ISO standards and continuously improve risk management.
Technical documentation
Writing and structuring of technical documents (TAD, QAP, project plans, vulnerability reports, security assurance plans) to capitalize and formalize your cloud practices.
/ Our compliance approach
We adopt a structured and progressive approach to secure your cloud environments, from initial audit to documentation and continuous compliance monitoring.
Initial audit
Evaluation of the existing cloud environment, resource mapping, and identification of gaps against GDPR, ISO requirements, and security best practices.
Risk analysis
Identification of cloud vulnerabilities, risk assessment (intrusion, crash, leaks), and prioritization by criticality and potential impact.
Action plan
Definition of corrective measures, development of the compliance roadmap, and governance policies adapted to your organization.
Compliance
Implementation of policies, deployment of security measures, and completion of remediation actions on your cloud environments.
Documentation & monitoring
Formalization of practices, writing of technical deliverables, and continuous compliance monitoring to maintain the required level over time.
/ Mastered cloud environments
We operate on the main hyperscalers and hybrid environments, adapting our governance and compliance practices to the specificities of each platform.
/
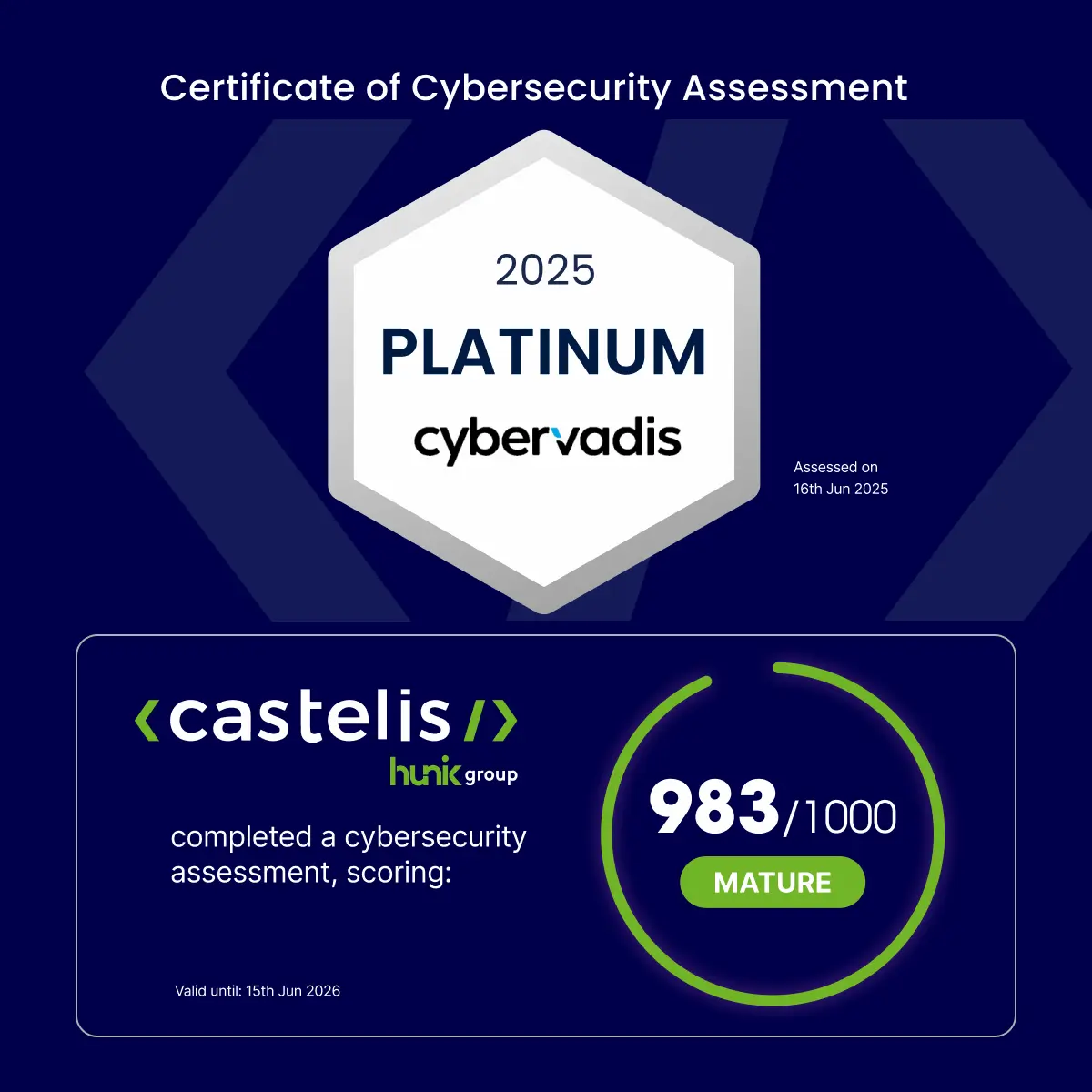
Compliance recognized by CyberVadis
Castelis obtained the CyberVadis 2025 Platinum medal with an exceptional score of 983/1000. This distinction attests to the high level of compliance, governance, and cloud risk management.
It recognizes our constant efforts to guarantee our clients secure, compliant environments aligned with international standards such as ISO 27001, GDPR, and NIST.
/
Frequently asked questions — cloud compliance
No, and it is often where the urgency arises. An unaudited production cloud environment accumulates invisible compliance debt. The sooner we intervene, the less costly and risky the remediation.
An internal CISO knows the context well but often lacks the perspective or availability for an end-to-end cloud compliance project. We intervene as a complement: external perspective, specific cloud expertise, and structured deliverables ready to be audited.
This depends on the complexity of the environment and the gaps identified. An initial audit with action plan is generally completed within a few weeks. Full compliance typically spans 2 to 6 months depending on the scope.
It serves three purposes: passing an audit (ISO, client, partner) without improvising, transferring knowledge in case of team changes, and having a reliable basis to evolve the architecture without regressing on compliance.
No. Your hosting provider’s certification covers their infrastructure, not your usage. How you configure your resources, manage access, and process data remains your responsibility. This is precisely what we audit.
Let's talk about your project

